Close Blind Spots In Your Security Data
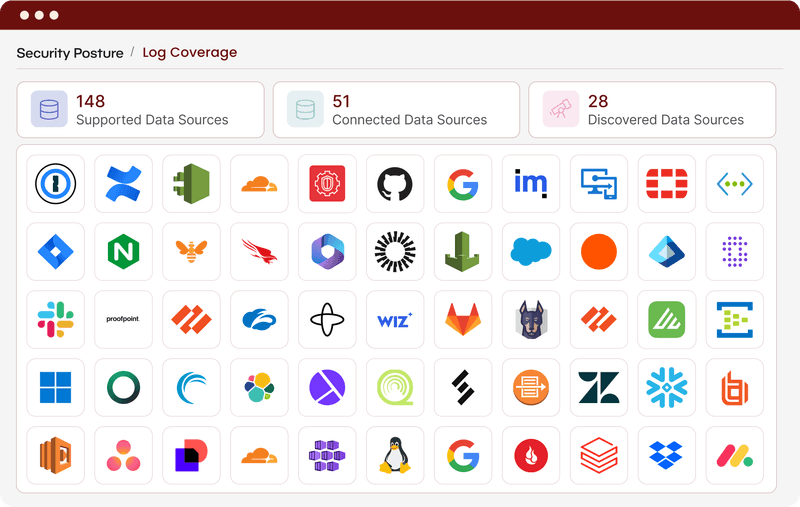
Every uncollected source is a place threats can hide. Beacon handles collection, normalization, and ongoing maintenance end to end, so expanding logging coverage is never bottlenecked by engineering effort.
The Impact on Your Security Program
Ensure decisions are security-driven
When adding a source is easy, coverage decisions become security decisions. Your data is collected and routed based on security value, not engineering capacity.

Close coverage gaps
Beacon continuously monitors that sources are collected, pipelines are healthy, and data is there when you need it.
Keep security teams on security work
Data onboarding, collection, routing and maintenance are handled out of the box using the industry’s largest content library and agentic workflows. Your team stays focused on what moves security forward.
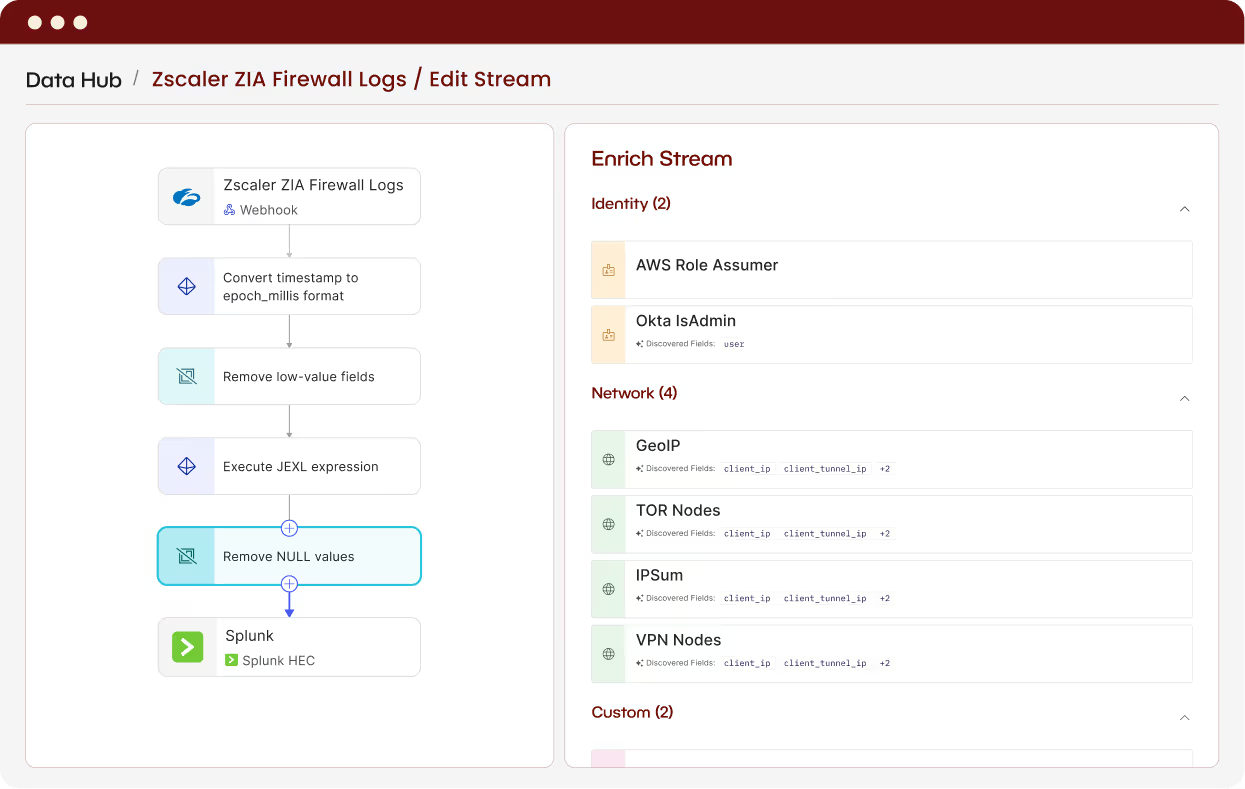
How Beacon Makes It Work
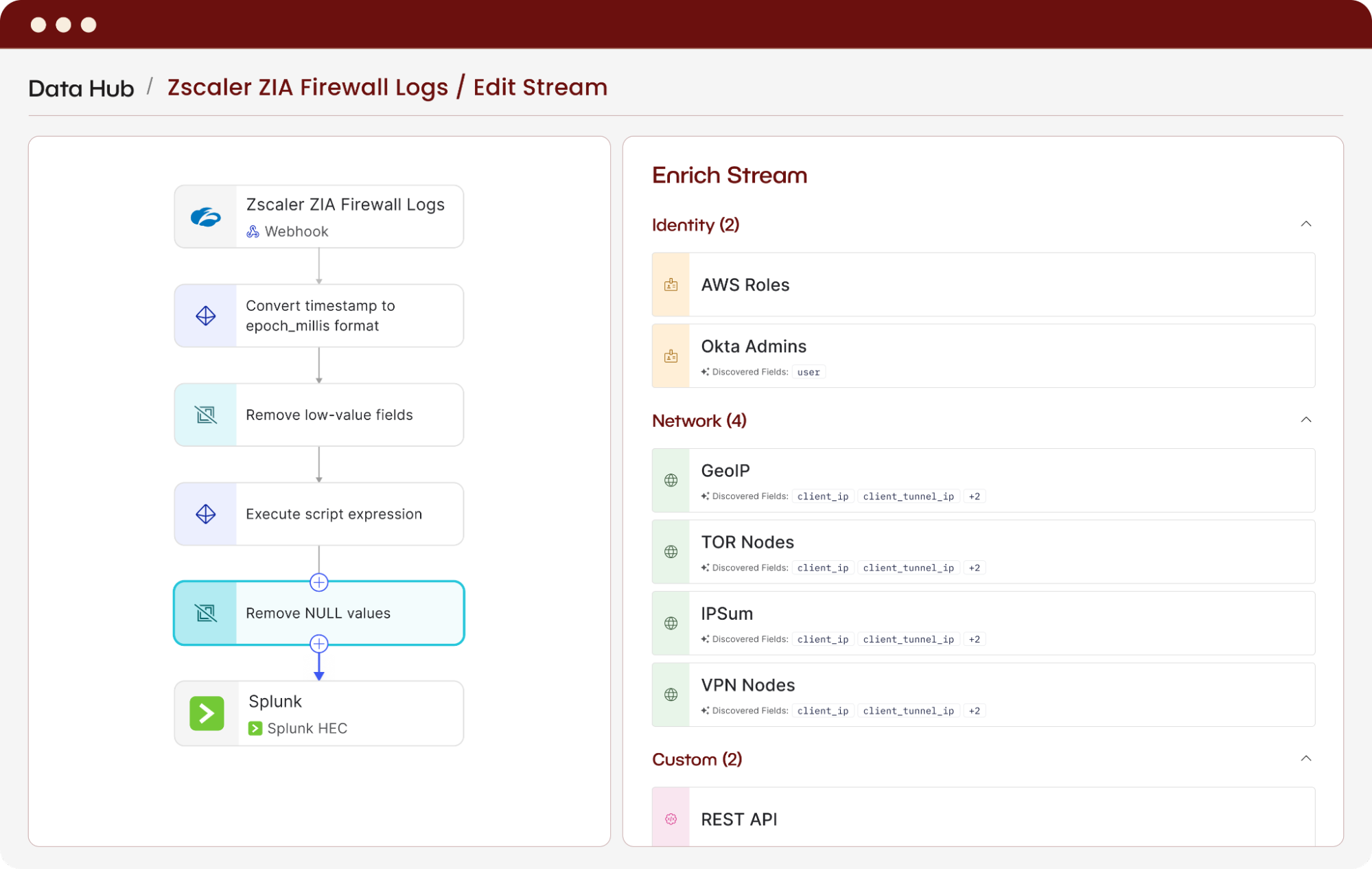
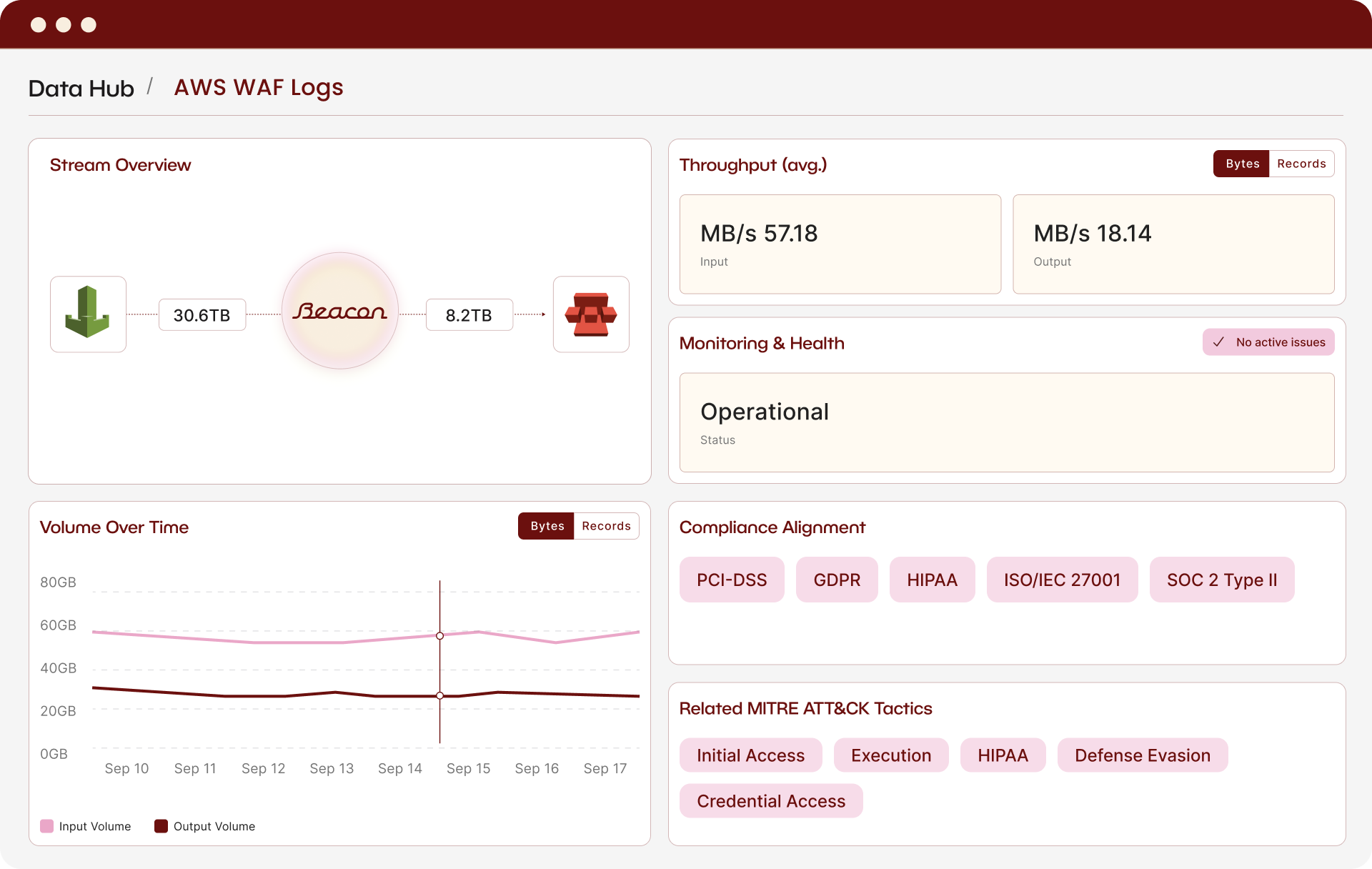
Beacon's security-driven data platform optimizes terabytes of important security logs spanning many sources. Data arrives enriched and normalized, and in the case of bloated VPC flow logs, reduced to 5% of their original size, enabling our security team and AI workflows to act immediately and effectively. We no longer choose between coverage and cost efficiency. We now have both, supported by a responsive team of security data experts.
Frequently Asked Questions
Security data coverage refers to how completely your environment is logged: which sources are actively collected, normalized, and available for detection and investigation. Poor coverage means threats can move through unmonitored systems without triggering alerts, and investigations hit dead ends where data should have been.
Most teams don't know until something goes wrong: an investigation stalls, a detection doesn't fire, or an audit reveals gaps. A more proactive approach is to map your environment against what should be logged and assign a coverage score. Beacon does this automatically, highlighting what's connected, what's missing, and what's drifting.
Start with sources tied to your highest-risk areas: identity providers, cloud environments, endpoint tools, and anything involved in authentication or privilege escalation. From there, layer in SaaS apps and business tools based on how they factor into your detection rules and compliance requirements. The key is to not let onboarding complexity dictate your priorities. If a source matters, it should be collected.
Every environment is different, but the sources teams tend to skip (SaaS apps, business tools) are often the ones attackers exploit. The real issue is that onboarding has traditionally been too complex and expensive to justify for every source. Tools like Beacon remove that friction, making it practical to collect broadly and optimize what gets sent where.
Beacon supports cloud environments, SaaS applications, business apps, identity providers, endpoint tools, and network security sources, with 100+ pre-built connectors and more added regularly.
Most sources can be onboarded in days using Beacon's pre-built connectors and normalization Recipes, compared to weeks or months with custom-built pipelines.
Beacon detects format changes and field additions automatically and adjusts the mappings. No manual remapping or engineering intervention is required.
Yes. Beacon supports custom connectors for proprietary or niche data sources, and new mappings can be generated quickly using Beacon's security research and AI capabilities.
Yes. You can route the same data stream to multiple destinations (your SIEM, a data lake, long-term storage) each normalized to the schema that destination expects.