Unlock AI SecOps
with reliable,
complete data
Beacon turns raw telemetry into data that defenders can act on. Structured for detection, enriched for investigation, optimized for scale and continuously maintained by AI.
Show me howYour data is failing your security operations
Attackers are weaponizing AI and moving at machine speed.
Manual data operations can't keep up.
Data overload and blind spots
Security teams are drowning in telemetry. There’s too much to store, too much to analyze – and the result is missed threats hiding in the noise.
Endless engineering upkeep
Unstructured, incomplete data produces results no one trusts. Teams are pushed back into manual work – the exact problem modernization came to solve.
Soaring costs, shrinking visibility
Every extra log blows up your SIEM bill, So you cut coverage to save money, and lose the context analysts and AI agents rely on.
Finally: security data that works for you.
Any source, any schema, any destination.
Any threat.
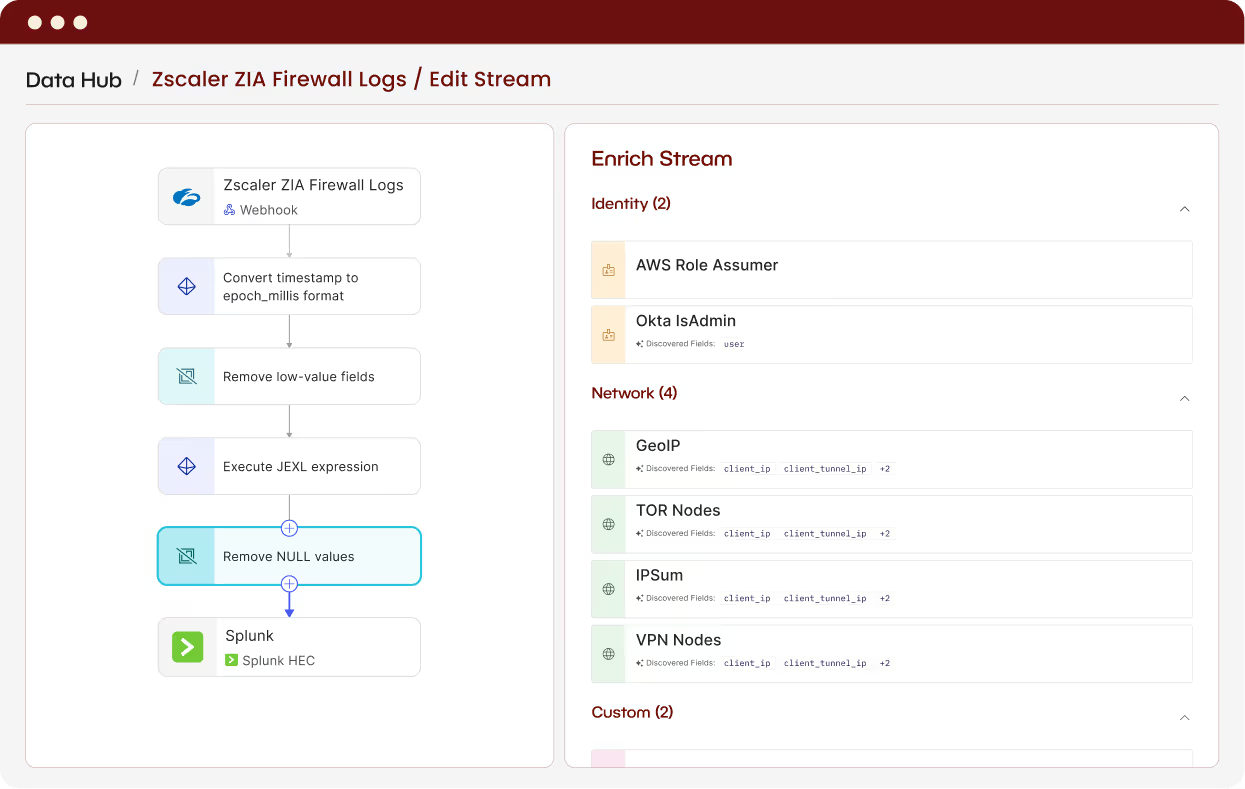
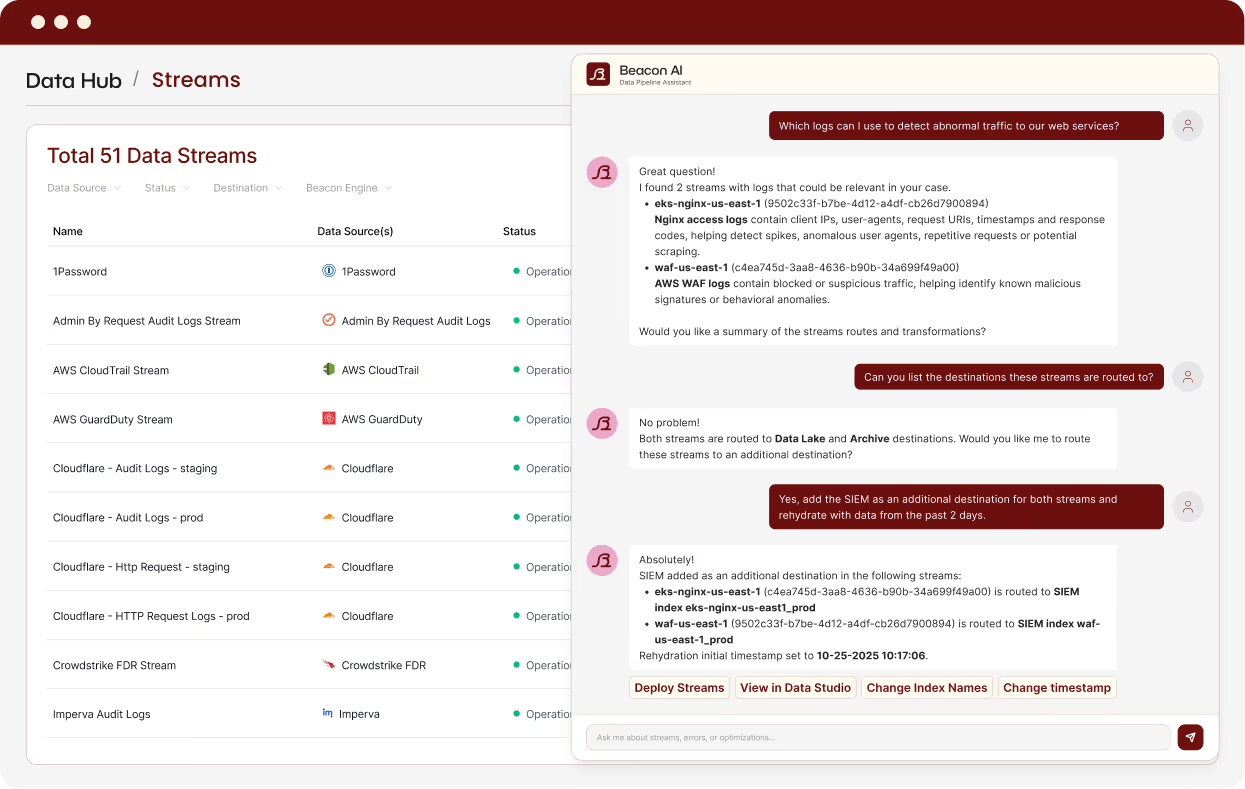
Investigate threats at machine speed
Events are normalized, enriched, and mapped leveraging AI before they reach your SOC. Analysts and agents get consistent, investigation-ready data from day one.
See what's missing before attackers do
AI agents map your environment, surface missing telemetry, and connect what’s broken. Coverage gaps close themselves before they become problems.
Reduce costs without losing coverage
AI-powered Recipes reduce volume without losing fidelity. Built on real attack data and vetted by security researchers, they preserve what actually matters.
Beacon
The AI-native

.png)
.png)
.png)
.png)
Beacon's security-driven data platform optimizes terabytes of important security logs spanning many sources. Data arrives enriched and normalized, and in the case of bloated VPC flow logs, reduced to 5% of their original size, enabling our security team and AI workflows to act immediately and effectively. We no longer choose between coverage and cost efficiency. We now have both, supported by a responsive team of security data experts.
Why Security Teams Choose Beacon
Built for AI from the ground up
From normalization to enrichment to routing to discovery, AI powers every stage, delivering structured, contextual data at speed and scale.
Security expertise baked in
Deploy production pipelines in minutes with expert-vetted optimization logic and enrichment strategies.
Enterprise-grade from day one
SOC 2 Type II and ISO 27001 compliant with multi-cloud, multi-region, and bring-your-own-cloud deployment options that meet your data residency and sovereignty requirements.
Beacon doesn’t just move logs around; it makes them
investigation-ready
security-optimized.